Excessive-severity Microsoft Change 0-day underneath assault threatens 220,000 servers
[ad_1]
Microsoft late Thursday confirmed the existence of two crucial vulnerabilities in its Change utility which have already compromised a number of servers and pose a critical danger to an estimated 220,000 extra around the globe.
The presently unpatched safety flaws have been underneath lively exploit since early August, when Vietnam-based safety agency GTSC found buyer networks had been contaminated with malicious webshells and that the preliminary entry level was some kind of Change vulnerability. The thriller exploit appeared nearly an identical to an Change zero-day from 2021 known as ProxyShell, however the clients’ servers had all been patched in opposition to the vulnerability, which is tracked as CVE-2021-34473. Ultimately, the researchers found the unknown hackers have been exploiting a brand new Change vulnerability.
Webshells, backdoors, and pretend websites
“After efficiently mastering the exploit, we recorded assaults to gather info and create a foothold within the sufferer’s system,” the researchers wrote in a submit revealed on Wednesday. “The assault staff additionally used numerous methods to create backdoors on the affected system and carry out lateral actions to different servers within the system.”
On Thursday night, Microsoft confirmed that the vulnerabilities have been new and mentioned it was scrambling to develop and launch a patch. The brand new vulnerabilities are: CVE-2022-41040, a server-side request forgery vulnerability, and CVE-2022-41082, which permits distant code execution when PowerShell is accessible to the attacker.
“Presently, Microsoft is conscious of restricted focused assaults utilizing the 2 vulnerabilities to get into customers’ programs,” members of the Microsoft Safety Response Middle staff wrote. “In these assaults, CVE-2022-41040 can allow an authenticated attacker to remotely set off CVE-2022-41082.” Group members harassed that profitable assaults require legitimate credentials for at the least one e-mail consumer on the server.
The vulnerability impacts on-premises Change servers and, strictly talking, not Microsoft’s hosted Change service. The massive caveat is that many organizations utilizing Microsoft’s cloud providing select an possibility that makes use of a mixture of on-premises and cloud {hardware}. These hybrid environments are as weak as standalone on-premises ones.
Searches on Shodan point out there are presently greater than 200,000 on-premises Change servers uncovered to the Web and greater than 1,000 hybrid configurations.
-
On-premises Change servers over time.
-
On-premises Change servers by geography.
-
Hybrid Change servers.
Wednesday’s GTSC submit mentioned the attackers are exploiting the zero-day to contaminate servers with webshells, a textual content interface that enables them to difficulty instructions. These webshells comprise simplified Chinese language characters, main the researchers to invest the hackers are fluent in Chinese language. Instructions issued additionally bear the signature of the China Chopper, a webshell generally utilized by Chinese language-speaking menace actors, together with a number of superior persistent menace teams identified to be backed by the Folks’s Republic of China.
GTSC went on to say that the malware the menace actors finally set up emulates Microsoft’s Change Net Service. It additionally makes a connection to the IP handle 137[.]184[.]67[.]33, which is hardcoded within the binary. Unbiased researcher Kevin Beaumont mentioned the handle hosts a pretend web site with solely a single consumer with one minute of login time and has been lively solely since August.
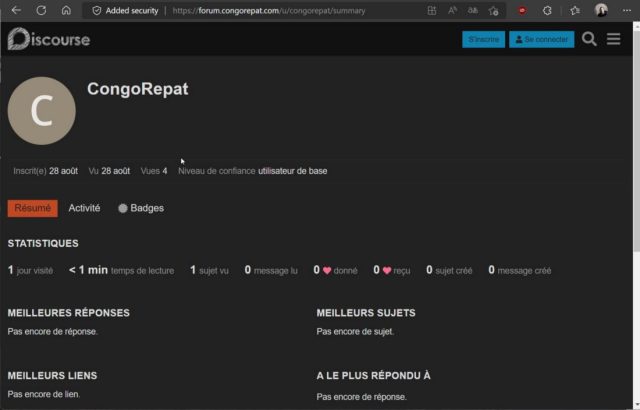
Kevin Beaumont
The malware then sends and receives information that’s encrypted with an RC4 encryption key that’s generated at runtime. Beaumont went on to say that the backdoor malware seems to be novel, which means that is the primary time it has been used within the wild.
Folks working on-premises Change servers ought to take quick motion. Particularly, they need to apply a blocking rule that forestalls servers from accepting identified assault patterns. The rule could be utilized by going to “IIS Supervisor -> Default Net Web site -> URL Rewrite -> Actions.” In the interim, Microsoft additionally recommends individuals block HTTP port 5985 and HTTPS port 5986, which attackers want to take advantage of CVE-2022-41082.
Microsoft’s advisory incorporates a number of different solutions for detecting infections and stopping exploits till a patch is obtainable.
Source link

